Crush-Ax-Injector is a a potent tool in the realm of kernel exploitation. This sophisticated framework enables malicious actors to force arbitrary code into the core functionality, potentially leading to full system takeover. Crush-Ax-Injector relies on vulnerabilities in the operating system's kernel to achieve its objectives. Security researchers are actively working to address the threats posed by Crush-Ax-Injector, striving to enhance system defenses and safeguard user data.
Evade Security Measures: A Deep Dive into Crush-Ax-Injector
Crush-Ax-Injector stands as a formidable tool within the realm of security exploitation. This devious framework empowers cybercriminals to infiltrate robust security measures, disrupting sensitive data and systems with alarming ease. At its core, Crush-Ax-Injector functions by leveraging a sophisticated combination of zero-days to gain unauthorized access. The tool's modular structure allows for extensive customization, making it highly adaptable against a wide spectrum of targets.
- Furthermore, Crush-Ax-Injector's ability to automate tasks {streamlines the exploitation process|, enabling faster and more efficient attacks.
Exploiting Root Privileges: The Power of Crush-Ax-Injector
Crush-Ax-Injector is a potent tool designed to acquire root privileges on targeted systems. This malicious software leverages vulnerabilities to override security measures, granting attackers complete control over the compromised machine. With root access, malicious actors can install any payload, steal sensitive data, or disrupt critical systems. Crush-Ax-Injector's refined nature poses a serious threat to system integrity and user privacy.
Injecting Arbitrary Code: Mastering Crush-Ax-Injector Techniques
Delve into the shadowy realm of manipulation, where skilled attackers wield the power of Crush-Ax-Injector techniques to inject more info arbitrary code onto unsuspecting systems. This thorough guide unveils the secrets behind these potent attacks, exploring their inner workings and providing practical insights into mitigation. From understanding the vulnerabilities that make them possible to dissecting the intricate mechanics of code injection, you'll gain a keen grasp of this critical security threat.
- Unveiling the Anatomy of Crush-Ax-Injector Attacks
- Building Effective Code Injection Vectors
- Protecting From Crush-Ax-Injector Threats
- Real-World Examples and Case Studies
Prepare to embark on a journey into the heart of code injection, where knowledge is power and vigilance is paramount.
Understanding the Crush-Ax-Injector Framework
The Whack-Ax-Insertion framework is a novel approach to optimizing application performance. It leverages a combination of techniques, including intense code optimization and runtime speedup, to achieve significant gains in processing speed and efficiency. This framework is particularly suited for applications that require high levels of speed, such as real-time systems, gaming applications, and data-intensive workloads.
- By examining the application's execution flow, Crush-Ax-Injector can identify performance issues that limit overall performance.
- Furthermore, it can dynamically modify code configurations to minimize overhead and maximize throughput.
Leveraging Advanced Techniques with Crush-Ax-Injector
Crush-Ax-Injector is a potent tool that facilitates advanced exploitation techniques. Attackers can harness its capabilities to inject malicious code into vulnerable systems, effectively hijacking their functionality. By leveraging system weaknesses, attackers can run arbitrary code, granting them access to sensitive data and potentially causing widespread damage. Crush-Ax-Injector's versatility makes it a popular choice for malicious actors seeking to breach security measures and achieve their objectives.
- Methods like code injection, privilege escalation, and remote code execution are all within the reach of skilled attackers utilizing Crush-Ax-Injector.
- Comprehending the intricacies of this tool is crucial for both defenders seeking to mitigate its impact and researchers striving to uncover new vulnerabilities.
The evolving landscape of cyber threats necessitates a vigilant approach to security. Remaining updated of advanced tools like Crush-Ax-Injector is essential for organizations to fortify their defenses and protect against increasingly sophisticated attacks.
 Jennifer Love Hewitt Then & Now!
Jennifer Love Hewitt Then & Now! Monica Lewinsky Then & Now!
Monica Lewinsky Then & Now! Tina Majorino Then & Now!
Tina Majorino Then & Now! Tyra Banks Then & Now!
Tyra Banks Then & Now!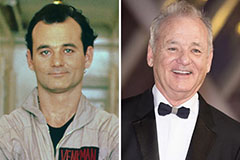 Bill Murray Then & Now!
Bill Murray Then & Now!